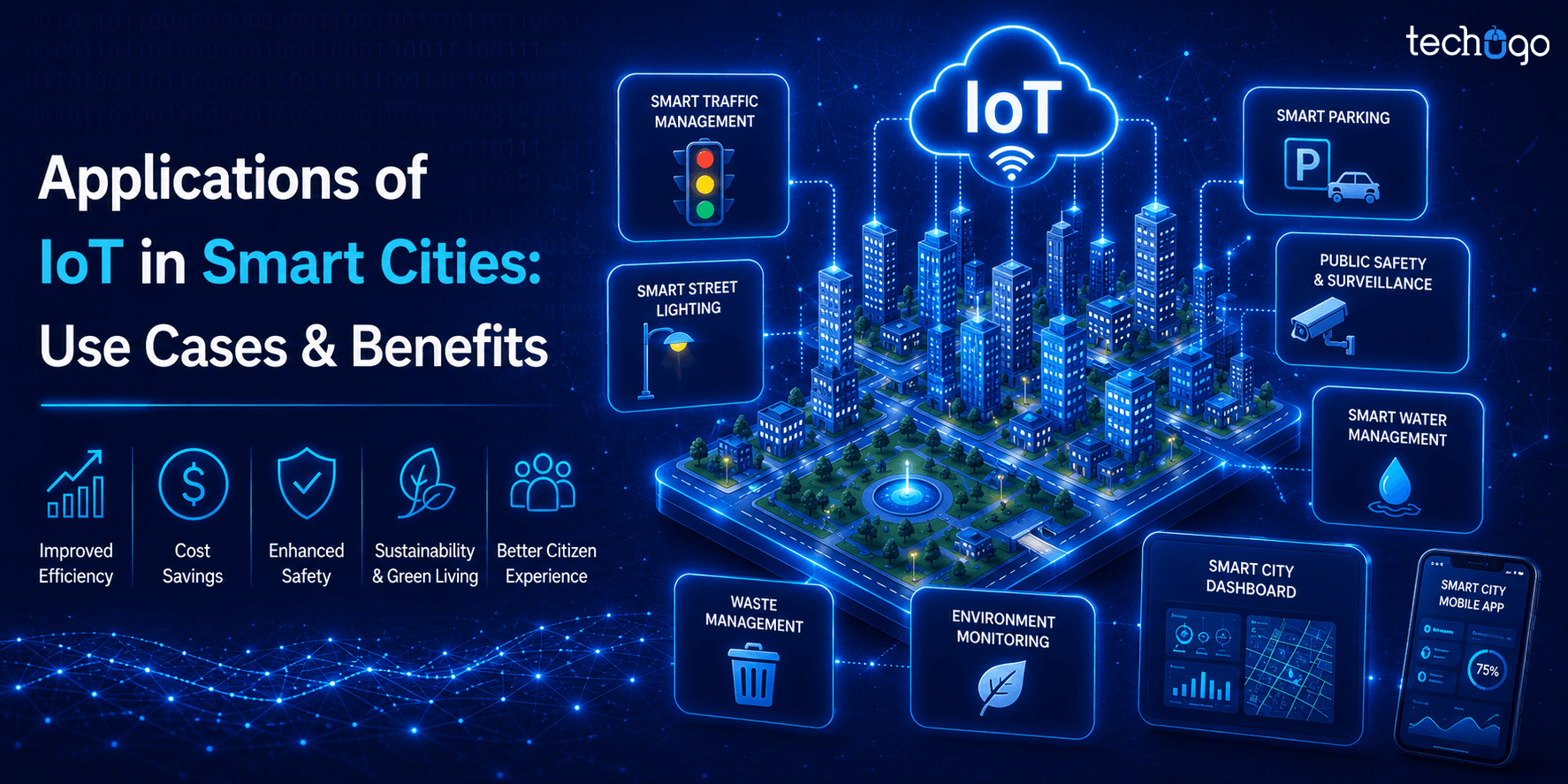
Long gone are the days when IT assets existed within a closed network and were easier to track. Now that people work across cloud platforms, remote work environments, mobile devices, SaaS applications, and connected IoT systems, assets are highly distributed and leading to difficulty in their management.
A recent research says that the average enterprise handles more than 165,000 cyber assets, including devices, cloud workloads, applications, users, and data systems. In many cases, there are over 500 digital assets for every employee that makes it nearly impossible to manually track assets.
The challenge does not stop there. As companies expand their digital infrastructure, the number of assets is continuously growing and studies show that enterprise cyber assets increased by over 130% in a single year.
Now it’s not easy to maintain visibility over every device, application, and system. When businesses lose track of their assets, they unknowingly create entry points for cyber threats and potential data breaches.
Fortunately, security teams are now gaining control of these assets and the associated risks through a mechanism called Cybersecurity Asset Management.
The approach helps security teams discover, monitor, and manage all digital assets across an organization’s infrastructure so that nothing slips through the cracks. Cybersecurity asset management lets businesses strengthen their overall security posture.
What does the security team do with it?
How does the mechanism benefit the startups and other businesses?
Are there any negative impacts of cybersecurity asset management?
If you’re looking forward to acquiring answers to these questions, you’ve landed at the right place! Therefore, we’ll talk about everything you need to know about cybersecurity asset management.
So, let’s get started.
What is Cybersecurity Asset Management

As cybersecurity expert Adrian Sanabria once said, “Most security and IT problems begin with visibility.” And this statement perfectly explains why organizations today prioritize cybersecurity asset management.
Cybersecurity asset management refers to the process of discovering, identifying, monitoring, and managing all digital assets within an organization’s IT environment so that potential security risks can be detected and addressed early. These assets may include devices, servers, cloud workloads, applications, databases, APIs, user accounts, and even connected IoT systems.
The core goal of cybersecurity asset management is simple: complete visibility. When security teams know exactly what assets exist in their ecosystem, they can identify vulnerabilities, track suspicious activity, and ensure that every system follows the organization’s security policies.
Without proper cybersecurity asset management, organizations often struggle with unknown or unmanaged assets, sometimes referred to as “shadow IT.” These hidden assets can easily become entry points for cyber attackers, putting sensitive data and critical infrastructure at risk.
This is why cybersecurity asset management plays a crucial role in a broader cybersecurity strategy. By continuously tracking assets and identifying potential gaps, businesses can reduce security blind spots, improve risk management, and strengthen their overall defense against cyber threats.
Also Read: How Dangerous Are Phishing, Pharming & Other Social-Engineering Attacks?
Why Must a Security Team Leverage Cybersecurity Asset Management?
As mentioned earlier, implementing cybersecurity asset management allows security teams to gain complete visibility into their organization’s digital infrastructure. When every device, application, and system is tracked properly, security professionals can detect vulnerabilities early and prevent potential threats before they escalate.
Beyond strengthening an organization’s security posture, cybersecurity asset management also delivers several operational and strategic benefits.
1. Automated Asset Monitoring and Policy Enforcement
One of the major advantages of cybersecurity asset management is automation. Modern asset management systems automatically identify assets that fail to comply with the organization’s security policies.
This allows security teams to quickly detect outdated software, unpatched systems, or unauthorized devices connected to the network. As a result, businesses can address vulnerabilities faster and maintain consistent security standards across their entire IT ecosystem.
2. Stronger Cloud Security
With businesses increasingly relying on cloud infrastructure, monitoring cloud assets has become essential. Cybersecurity asset management helps organizations locate cloud instances, workloads, or applications that may not have been scanned for vulnerabilities.
By identifying misconfigured cloud resources or unmonitored environments, security teams can reduce the risk of data exposure and ensure that all cloud assets remain protected.
3. Reduced Attack Surface
Another important benefit of cybersecurity asset management is reducing the organization’s attack surface. When unknown or unmanaged assets remain hidden within an IT ecosystem, they often become easy entry points for cyber attackers.
Through continuous asset discovery and monitoring, security teams can identify unused systems, vulnerable endpoints, or shadow IT resources. By securing or eliminating these assets, organizations significantly minimize potential attack vectors.
4. Smooth Integration of New IT Resources
Organizations continuously introduce new technologies, tools, and infrastructure into their digital ecosystem. Without proper asset visibility, these additions can create security gaps.
A robust cybersecurity asset management system ensures that every new asset entering the network is discovered, categorized, and evaluated for risks. This allows businesses to adopt new technologies without disrupting their security framework and enables faster, more confident decision-making.
5. Faster Threat Detection and Response
Cybersecurity asset management also enables a proactive security approach. By maintaining a real-time inventory of all assets, security teams can quickly identify suspicious activity, unauthorized devices, or unusual system behavior.
This early detection capability helps organizations respond to potential security incidents before they evolve into major cyberattacks, significantly reducing the impact of breaches and improving overall incident response.
6. Improved Compliance and Risk Management
Organizations today must comply with multiple cybersecurity regulations and industry standards. Without a complete inventory of digital assets, maintaining compliance becomes extremely challenging.
Cybersecurity asset management helps businesses track every device, system, and application across their infrastructure. This enables security teams to monitor compliance requirements, conduct regular audits, and ensure that all assets adhere to established security policies and regulatory standards.
What are the Challenges of Cybersecurity Asset Management?

Are you responsible for managing, tracking, and securing the assets? Then, you might have faced a fair share of challenges.
While cybersecurity asset management plays a critical role in strengthening an organization’s security posture, implementing and maintaining it is not always straightforward. Security teams are often responsible for discovering, monitoring, and protecting thousands of digital assets across complex infrastructures.
Without proper asset discovery tools and continuous monitoring, maintaining complete IT asset visibility becomes difficult. As a result, organizations face several operational and security challenges while managing their cyber assets.
Let’s explore some of the most common challenges and their possible solutions.
1. Locating Unmanaged or Unknown Devices
One of the biggest challenges in cybersecurity asset management is identifying unmanaged devices. These are devices that connect to a network but are not registered in the organization’s asset management system or do not have security agents installed.
Such devices often become blind spots for security teams and can easily expand the organization’s attack surface.
- Solution:
Organizations must adopt automated asset discovery and monitoring solutions that collect data from networks, endpoints, and agent-based security tools. Continuous asset discovery ensures that every device connected to the network is identified and monitored in real time.
2. Maintaining an Accurate Asset Inventory
Creating and maintaining a complete cyber asset inventory can be challenging, especially when organizations frequently add new systems, applications, and devices. The rise of IoT devices, remote work infrastructure, and mobile endpoints has further complicated asset tracking.
Without accurate inventory data, security teams cannot effectively perform vulnerability management or risk assessment.
- Solution:
Businesses should implement centralized digital asset inventory platforms that automatically update asset information and allow customizable data aggregation intervals. This helps security teams maintain an accurate and up-to-date view of their IT ecosystem.
3. Managing Cloud and SaaS Asset Sprawl
Modern organizations rely heavily on cloud platforms and SaaS applications, which often leads to the rapid expansion of digital assets. Many cloud workloads, APIs, or third-party integrations remain untracked, creating security blind spots.
This lack of visibility weakens cybersecurity asset management strategies and increases the chances of misconfigured resources.
- Solution:
Security teams should integrate cloud asset discovery tools that continuously scan cloud environments and SaaS platforms to identify unmonitored assets, detect vulnerabilities, and strengthen overall attack surface management.
4. Evaluating Compliance and Regulatory Requirements
Organizations must comply with numerous cybersecurity regulations and industry standards. However, in the absence of a comprehensive asset inventory, it becomes difficult to determine whether all devices and applications meet compliance requirements.
This can lead to compliance gaps, security violations, and potential legal risks.
- Solution:
Businesses should align their cybersecurity asset management framework with compliance monitoring tools. Continuous auditing and automated reporting ensure that every digital asset adheres to security policies and regulatory standards.
5. Shadow IT and Unauthorized Applications
Another major challenge is shadow IT, where employees use unapproved software, applications, or devices without the knowledge of the IT department. These hidden assets increase vulnerability and complicate asset monitoring.
Shadow IT has become even more common with remote work environments and the rapid adoption of SaaS tools.
- Solution:
Organizations must implement continuous asset discovery and usage monitoring systems that detect unauthorized applications and devices. Security teams can then classify and control these assets before they become security risks.
6. Managing Security Across Mobile and Application Ecosystems
Modern organizations also rely heavily on mobile applications and connected platforms, which introduce additional cybersecurity risks. Mobile devices, APIs, and backend systems must be tracked as part of the organization’s cyber asset inventory.
Without proper monitoring, these assets can expose sensitive data and user information.
- Solution:
Partnering with a trusted mobile app development company can help businesses design secure applications with integrated asset monitoring, endpoint security, and data protection strategies.
Additionally, organizations are increasingly collaborating with a generative AI consulting company to build intelligent security systems that automate asset discovery, risk detection, and vulnerability prioritization.
By addressing these challenges with the right strategies and tools, organizations can significantly improve the effectiveness of their cybersecurity asset management framework and maintain stronger protection against evolving cyber threats.
Why Must an Organization Prioritize Cybersecurity Asset Management?
Traditionally, businesses never emphasized cybersecurity asset management since the tools required for automating the processes never existed. IT environments were smaller, infrastructures were largely on-premise, and asset inventories could be maintained manually with reasonable accuracy.
But the modern digital ecosystem has changed dramatically. Organizations now operate across cloud platforms, SaaS applications, mobile devices, APIs, and distributed work environments. As a result, the number of digital assets within an enterprise has multiplied significantly, making manual tracking nearly impossible.
From a security standpoint, this lack of visibility creates one of the biggest risks in cybersecurity: unknown assets. Security teams often refer to this as the “visibility gap.”
If an organization does not know what devices, applications, or services exist within its environment, it cannot properly secure them. Untracked assets frequently become the weakest link in the security chain and are often exploited by attackers.
This is where cybersecurity asset management becomes critical. By continuously discovering, cataloging, and monitoring every digital asset within an organization’s infrastructure, businesses gain the visibility required to identify vulnerabilities, enforce security policies, and reduce their overall attack surface.
Another practical reason organizations prioritize cybersecurity asset management is the need for continuous monitoring. Modern IT environments evolve rapidly—new devices connect to networks, new applications are deployed, and cloud resources are created or modified daily. Without automated asset discovery and monitoring systems, security teams would struggle to keep pace with these constant changes.
Importantly, cybersecurity asset management is not limited to technology companies. Any organization that relies on hardware, software, or connected systems must prioritize asset visibility and protection.
For example, manufacturing companies operate complex industrial control systems, machinery, and connected production equipment. If these assets remain unmonitored or poorly secured, they can become entry points for cyber threats that disrupt operations or compromise sensitive data.
In practice, organizations that prioritize cybersecurity asset management gain a clear advantage. They are able to detect vulnerabilities faster, respond to threats more effectively, and maintain stronger control over their digital infrastructure.
In today’s era, where cyberattacks increasingly target overlooked systems and misconfigured resources, maintaining complete asset visibility is a must and a foundational requirement..
Best Practices for Cybersecurity Asset Management in 2026

Cybersecurity asset management demands coming together of numerous processes. For businesses to take complete advantage of the system, they must be able to recognize, access, and mark any security risks associated with their assets while taking the necessary steps.
Additionally, they must be able to monitor any assets in real-time and segregate the untrusted ones from the rest.
Below are some practical best practices organizations should follow in 2026 to strengthen their cybersecurity asset management strategy.
1) Start with Continuous Asset Discovery
The first rule of effective cybersecurity asset management is simple: you cannot secure what you cannot see. Organizations must continuously discover every asset connected to their environment, including endpoints, servers, cloud workloads, SaaS applications, and APIs.
Automated asset discovery tools help security teams detect new devices or applications the moment they enter the network, reducing blind spots and improving overall IT asset visibility.
2) Maintain a Single Source of Truth for Assets
Many organizations struggle with fragmented asset data stored across multiple systems. This makes security monitoring difficult and often leads to incomplete asset inventories.
A centralized cyber asset inventory allows security teams to maintain a single, continuously updated record of all digital assets. This ensures that every device, application, and system is properly tracked and monitored across the organization.
3) Classify Assets Based on Risk and Criticality
Not every asset carries the same level of risk. Some systems store sensitive data, while others support critical business operations.
Security teams should classify assets based on factors such as data sensitivity, system exposure, and business impact. This enables organizations to prioritize protection for high-risk assets and allocate cybersecurity resources more effectively.
4) Integrate Asset Management with Vulnerability Monitoring
Cybersecurity asset management becomes far more powerful when integrated with vulnerability management tools.
By linking asset inventory with vulnerability scanners, security teams can quickly identify which systems have outdated software, missing patches, or security misconfigurations. This approach helps organizations respond to risks faster and reduce their attack surface.
5) Keep a Close Eye on Cloud and SaaS Assets
Cloud infrastructure and SaaS platforms are expanding rapidly across modern organizations. Unfortunately, these environments often contain misconfigured resources or forgotten applications that become security risks.
Continuous monitoring of cloud workloads, APIs, and SaaS tools ensures that organizations maintain visibility into these assets and quickly detect vulnerabilities before attackers exploit them.
Must Read: Must-Have SaaS Security Best Practices to Win Over Enterprise Clients
6) Use AI to Strengthen Asset Visibility
As digital environments grow more complex, many organizations are adopting AI-driven security solutions to automate asset discovery and risk detection. Working with a trusted generative AI development company can help businesses build intelligent systems that continuously analyze infrastructure, identify unknown assets, and prioritize security threats.
For companies that rely heavily on mobile platforms, partnering with an experienced app development company also ensures that application ecosystems are designed with strong security monitoring and asset management capabilities.
By implementing these best practices, organizations can transform cybersecurity asset management from a basic inventory process into a proactive security strategy that strengthens visibility, reduces vulnerabilities, and protects digital infrastructure against evolving cyber threats.
To Sum Up…
Security providers of today emphasize implementing asset management for a healthier business ecosystem. Moreover, it enables security providers to improve the overall cloud resources and supports the firm’s efficiency. Fortunately, it also tracks down any potential issues before they escalate into major security breaches.
Now that you have enough reasons for implementing cybersecurity asset management into your business, what is your take on the idea?
It is essential to mention that compromising with asset management practices can shoot up the chances of disrupting business operations, putting the organization at stake. Therefore, poor asset management operations are to be strictly avoided.
Have you thought this through?
If that’s a yes, reach out to the experts for more insights on the idea!
Get in touch
We'd love to hear from you.



 SA
SA  KW
KW  IE
IE AU
AU UAE
UAE UK
UK USA
USA  CA
CA DE
DE  QA
QA ZA
ZA  BH
BH NL
NL  MU
MU FR
FR